It is tough to decide on that wireless apparatus to successfully remove in the event that you have an exact record to start with. That is certainly why the PCI Council lets you “scanning all of card data natural atmosphere locations such as HP Access Point Price List accessibility apparatus and continue maintaining anup-to-date inventory”
If there is anything that we all understand about robots, it truly is they’re always stripping off in our partitions. Do not ever presume you are safe as you are ‘way too little’ to get a newbie to take care of. Hackers need info, of course should they look for a weak spot which permits them to put in a simple entry level, they will take action. That is certainly the reason funding is not ever a spot at time. It is a Practice.
The pci-dss says that most associations ought to scan for rogue wireless access issues Rest. But do not allow this demand frighten you by scanning often. The greater your own scanning frequency, the timelier the own results.
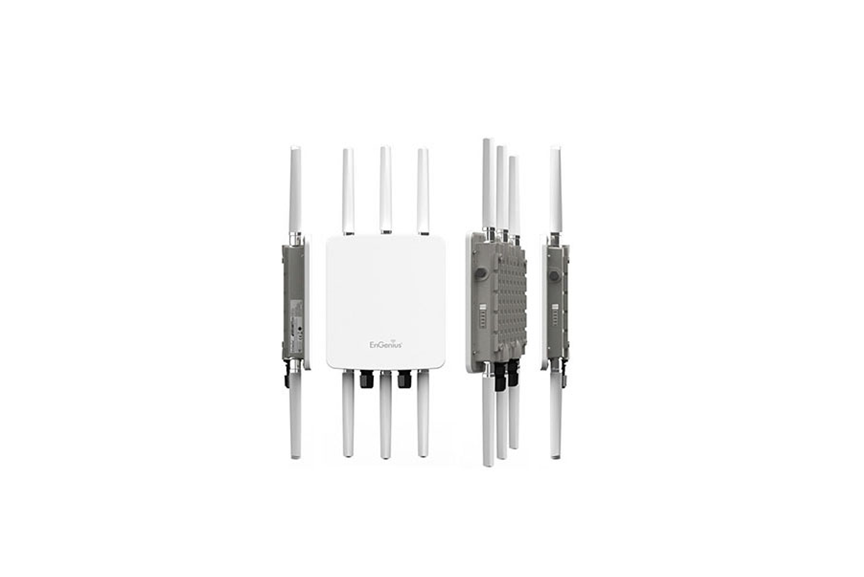
Access pointsapplicationsetup
As soon as you select your application, it truly is time to get setup. Installation of an invisible scanning apparatus is not too sophisticated, however it is crucial that you regard the program’s connection direction and alerting features. You have to empower automatic alarms and also a containment mechanism to eradicate unlicensed wireless issues.
When you exemplify wireless access points into a system diagram or only write a first record, then you also have to record business explanation for every wireless access level. In the event that you can’t ever warrant the accessibility level’s presence, then you have to disable it. In the event that you actually wonder whether an entry stage is untrue or exactly that which it really is accomplishing in a particular space, then you should only seek advice from your organization rationale checklist.
But in case a scanning did look for that a valid rogue wireless access stage, “businesses should instantly fix the Allied hazard in view of pci-dss prerequisite 12.9 and then re-scan the surroundings in the first possible prospect.”
- Measure 3: Pick on which to scan, then scan your own surroundings
- Measure 4: Remediate any discovered rogue access Factors
Perhaps not every alarm your scan explains is always untrue. Your scanning might possibly have seen false-positives. On occasion a scanner may determine an entry stage as simple if your waiter assigns an ip to some brand-new, valid employee notebook. Documentation is critical to learn whether your false good is extremely bogus or something to check farther in to.
Fix points installedwireless access
Considering that a fictitious apparatus can possibly appear at just about any component of one’s own environment, it is crucial that you focus on where you are scanning. As stated by the PCI DSS, either “destinations that save, process or transmit cardholder info [should be manually] scanned routinely or [a] Wi-Fi IDS/IPS [needs to be] executed in these areas”
If you wind up obtaining rogue access points installed on your employees, this is a terrific moment and energy for you to write or apply unauthorized entry level limitation and result insurance guidelines.
- Measure 5: maintain a routine scan program
- Measure Two for a scanning instrument also properly configure it
When you hunt for that most suitable instrument, be certain it truly is wireless, yet maybe completely wired. Wired scanning programs have been all employed by a number of associations to get extra stability, however based to this pci-dss they possess a higher false positive speed and cannot assist you to adhere to demand 11.1.
This really is the point where a system card or map data stream diagram arrives right into drama with. (You ought to have these programs recorded (according to pci-dss prerequisite 1.1.3). This will reveal to you the way memory data goes inside of your own environment and assist you to examine precisely what elements you have to scan depending about the areas which save, process, or transmit cardholder information.
In the event that you are a little business company along with all of your systems squeeze to one stand on your information centre, this condition ought to really be pretty simple, a fast appearance would spot hardware that is unknown. If you should be a wide spread business, then it is going to simply consider an extra hours.
As a way to overcome rogue wireless programs, just employ a wireless speaker or even wireless intrusion detection/prevention platform (IDS/IPS). (The PCI Council urges large associations utilize an IDS/IPS technique)
Additionally, this is a fantastic period to make sure you have emotionally procured your wireless apparatus so that they really aren’t accessible for the overall people.
I urge wireless scanning and IDS technology such as Fluke Networks Air Magnet, Snort (Open source), Notify Logic, along with Cisco.

